PowerShell security measures you should know about
I use PowerShell a lot to make life easier as a developer. Also for system administrators PowerShell can be a great solution for various tasks. There are little things that cannot be done using PowerShell when you would compare it to for example an executable file. Microsoft made some security measures to protect you from running any malicious PowerShell scripts and in this article I will summarise the information I found regarding this topic.
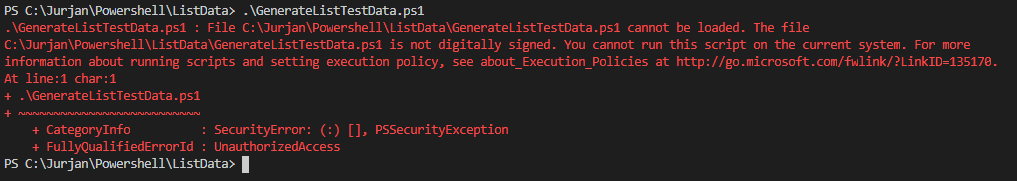
File cannot be loaded because of Execution Policies
When you are also working with PowerShell it will not take long until you will see an error message like displayed below. If this happens then I have some good news! you are well protected. 😆 Seriously, PowerShell scripts should be treated as ordinary executable files and you would never run an executable that you grabbed from the internet without some serious doubts… now would you?
.\GenerateListTestData.ps1 : File C:\Jurjan\Powershell\ListData\GenerateListTestData.ps1 cannot be loaded because running scripts is disabled on this system. For more information, see about_Execution_Policies at
Now that we know that windows protects us from running potential harmful scripts, the most common question on the internet is: how can I avoid getting this security warning followed by the most common answer: set the execution policy to unrestricted. Although it can be a solution to set the execution policy to unrestricted. Knowing what you are doing is better than just following this advice blindly. Microsoft had described this policy here [click to open] which you should read for a detailed understanding.
Scenario
In this scenario I download one of my own scripts, to do the same you can click the ‘open raw button’ on the bottom of the page: generateListData. I assure you, nothing bad will happen.
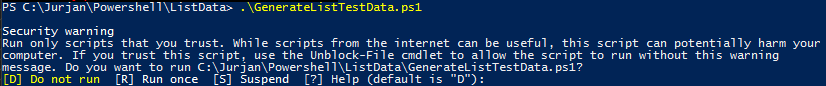
Now because I have not signed this file, you will probably also get a warning message as displayed below:
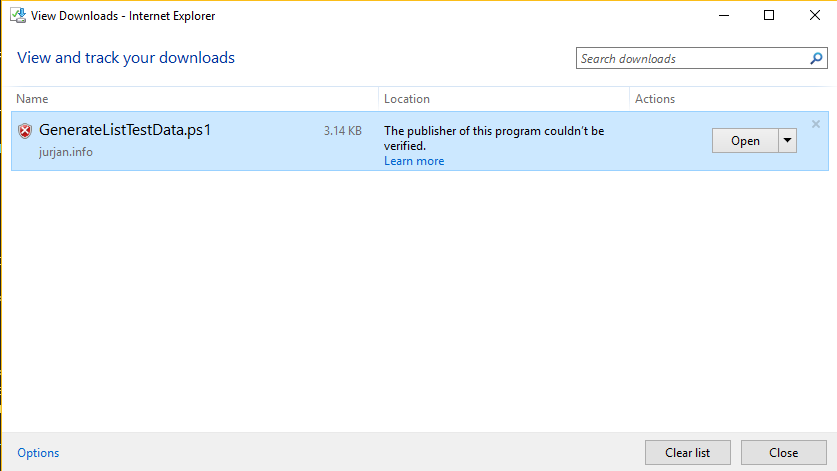
Basically, this means, you downloaded a potentially harmful file because its origin is unknown.
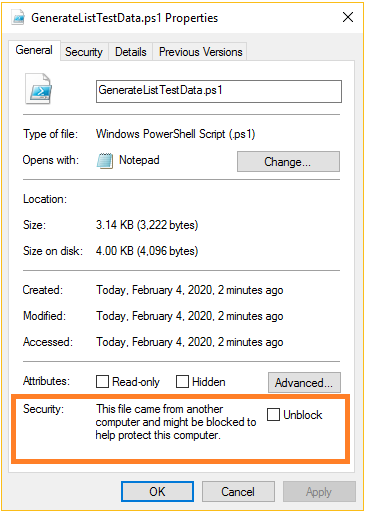
Now when you check the properties of the file, you will notice that the file has been blocked as a security measurement. Now lets see what happens if we will try to execute the PowerShell script.
First we need to check what the actual execution policy is set to on the computer. We can do this by using the following PowerShell command Get-ExecutionPolicy:
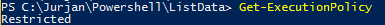
And as you can see I have set it to Restricted. Restricted doesn’t load configuration files or run scripts. This is the default execution policy for Windows client computers.
Click here to see all the options available
The acceptable execution policy values are as follows:
a) AllSigned. Requires that all scripts and configuration files are signed by a trusted publisher, including scripts written on the local computer.
b) Bypass. Nothing is blocked and there are no warnings or prompts.
c) Default. Sets the default execution policy. Restricted for Windows clients or RemoteSigned for Windows servers.
d) RemoteSigned. Requires that all scripts and configuration files downloaded from the Internet are signed by a trusted publisher. The default execution policy for Windows server computers.
e) Restricted. Doesn't load configuration files or run scripts. The default execution policy Windows client computers.
f) Undefined. No execution policy is set for the scope. Removes an assigned execution policy from a scope that is not set by a Group Policy. If the execution policy in all scopes is Undefined, the effective execution policy is Restricted.
g) Unrestricted. Beginning in PowerShell 6.0, this is the default execution policy for non-Windows computers and can't be changed. Loads all configuration files and runs all scripts. If you run an unsigned script that was downloaded from the internet, you're prompted for permission before it runs.
It should be no surprise that when I try to execute this script that I will get the error mentioned in the introduction.
When we set the execution policy to unrestricted using Set-ExecutionPolicy Unrestricted and try to execute a blocked PowerShell we will see the following error message which got me quite puzzled until I now know that in such situations the file is blocked.
Once we unblock the file, using the checkbox of the file properties, we can finally run the script without any warnings. Another way to unblock scripts is to use the Unblock-File cmdlet.
Finally, when the execution-policy is set to RemoteSigned any blocked file will get the error message (so not even the security-warning) and all unblocked files will be executed without any warnings.
Final words
When working with PowerShell scripts I would advice to set the execution-policy to RemoteSigned and never to Unrestricted. This way any unblocked file can be executed, while blocked files have to be unblocked first. Always open the script first to see what it does before executing.